Hi, I'm Erick Sanga
Cybersecurity Professional | Penetration Tester | Threat Hunter
Securing digital assets and exploring the evolving landscape of cybersecurity with expertise and innovation.

Securing digital assets and exploring the evolving landscape of cybersecurity with expertise and innovation.

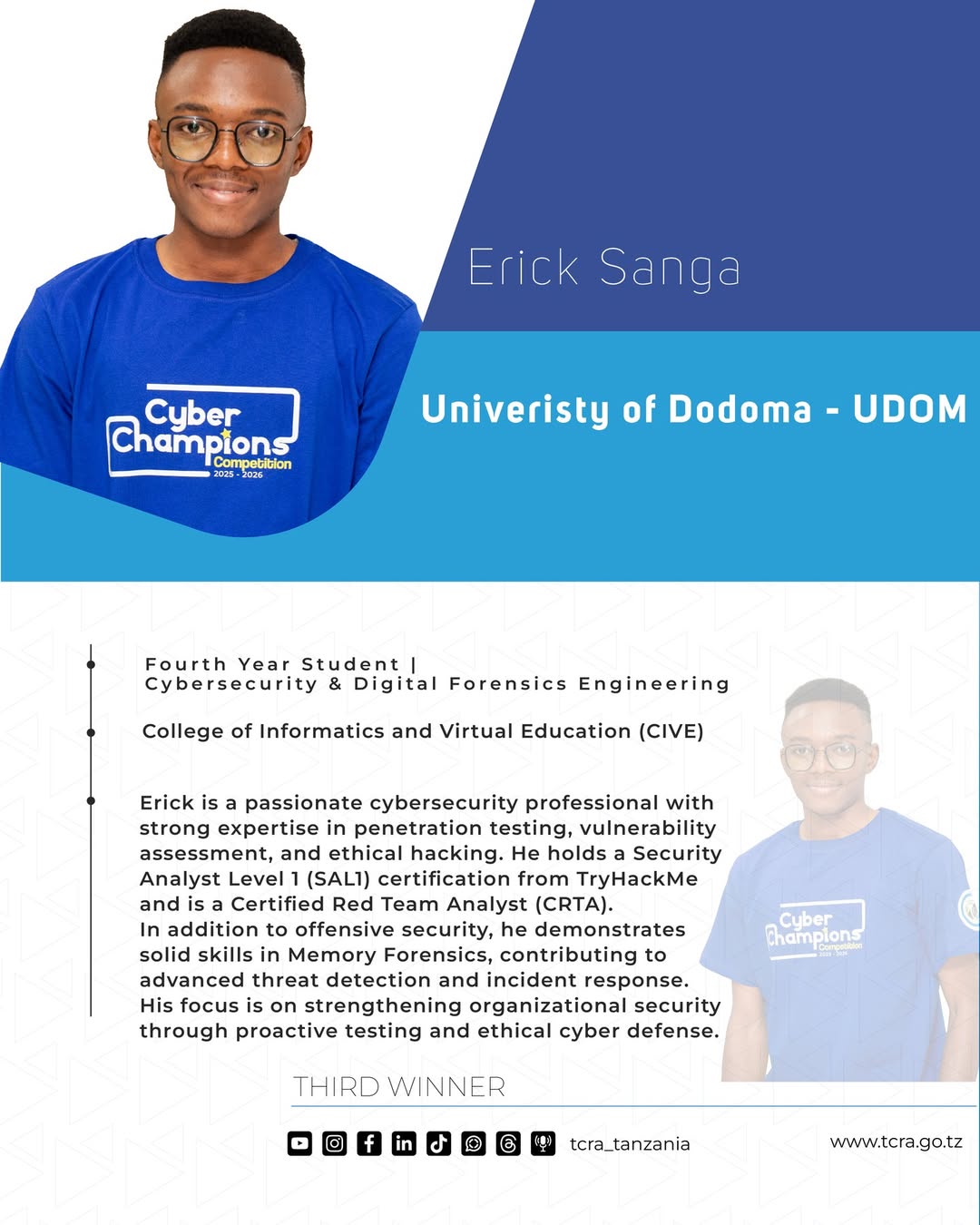
I'm final year Cybersecurity and Digital Forensics Engineering student passionate about protecting digital infrastructures and solving security challenges. My journey in this field has been driven by curiosity and a commitment to making the enhancing the security and resilience of digital infrastructures.
I am committed to expanding my skills in penetration testing, threat detection, and system hardening while adapting to emerging technologies. With a strong focus on industry-oriented solutions, my goal is to build a solid foundation in cybersecurity and grow into a productive security professional.
Name:
Erick Sanga
Education:
Bsc. Cybersecurity and Digital Forensics Engineering - University of Dodoma 2022-Present
Experience:
Cybersecurity practitioner
Freelance:
Available

I created a practice linux terminal simulator that helps cybersecurity enthusiasts master linux command recognition, learn correct flag usage and track your progress as you go.

I created a curated collection of cybersecurity resources to answer the famous question "Where do I start?", courses, tools, platforms, communities, and career paths all in one place.

I created a real-time global intelligence dashboard — AI-powered news aggregation, geopolitical monitoring, and infrastructure tracking in a unified situational awareness interface.

Send files securely with military-grade AES-256 encryption and an intuitive GUI. Password-protected transfers that even snoops can't crack.

I created a keystroke monitoring tool using python programming language that sends keystrokes to the controller's server. It works for both windows and linux operating systems.

Detect vulnerabilities, test resilience—simulate WiFi deauthentication attacks to secure networks before attackers do.

This is an intentionally vulnerable Ubuntu Linux virtual machine designed for security training and penetration testing practice.I methodically exploited its weaknesses, demonstrating a common penetration testing lifecycle: Reconnaissance, Enumeration and Exploitation.

This project focuses on penetration testing of the Damn Vulnerable Web Application (DVWA), a deliberately insecure web application designed for security professionals and ethical hackers to practice vulnerability assessment. The testing includes SQL Injection, Cross-Site Scripting (XSS), Command Injection, CSRF, and authentication bypass techniques. The goal is to identify and exploit security weaknesses while implementing best practices for web application security hardening.

OWASP Juice Shop is probably the most modern and sophisticated insecure web application.The application contains a vast number of hacking challenges of varying difficulty where the user is supposed to exploit the underlying vulnerabilities.Juice Shop encompasses vulnerabilities from the entire OWASP Top Ten along with many other security flaws found in real-world applications!